XEN网络配置综述
2012-06-03 17:37:06 来源: 评论:0 点击:
在dom0上运行iptables -L 应显示以下相似内容:
dom0:~# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination ACCEPT 0 -- 10.0.0.1 anywhere PHYSDEV match --physdev-in vif1.0 ACCEPT udp -- anywhere anywhere PHYSDEV match --physdev-in vif1.0 udp spt:bootpc dpt:bootps Chain OUTPUT (policy ACCEPT) target prot opt source destination
在dom0上运行route 应显示以下相似内容:
dom0:~# route Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 10.0.0.1 * 255.255.255.255 UH 0 0 0 vif1.0 192.168.0.0 * 255.255.255.0 U 0 0 0 eth0 default 192.168.0.1 0.0.0.0 UG 0 0 0 eth0
在domU上运行ifconfig 应显示以下相似内容:
vm01:~# ifconfig
eth0 Link encap:Ethernet HWaddr 00:16:3E:4B:2F:21
inet addr:10.0.0.1 Bcast:10.0.0.255 Mask:255.255.255.0
inet6 addr: fe80::216:3eff:fe4b:2f21/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:144 errors:0 dropped:0 overruns:0 frame:0
TX packets:129 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:17774 (17.3 KiB) TX bytes:15478 (15.1 KiB)
双向路由网络模式
此xen配置相对复杂一些. 转发规则均须手工设置.这个配置当然有更大的弹性,其允许建立私有网络并进行路由.
网络结构示意图
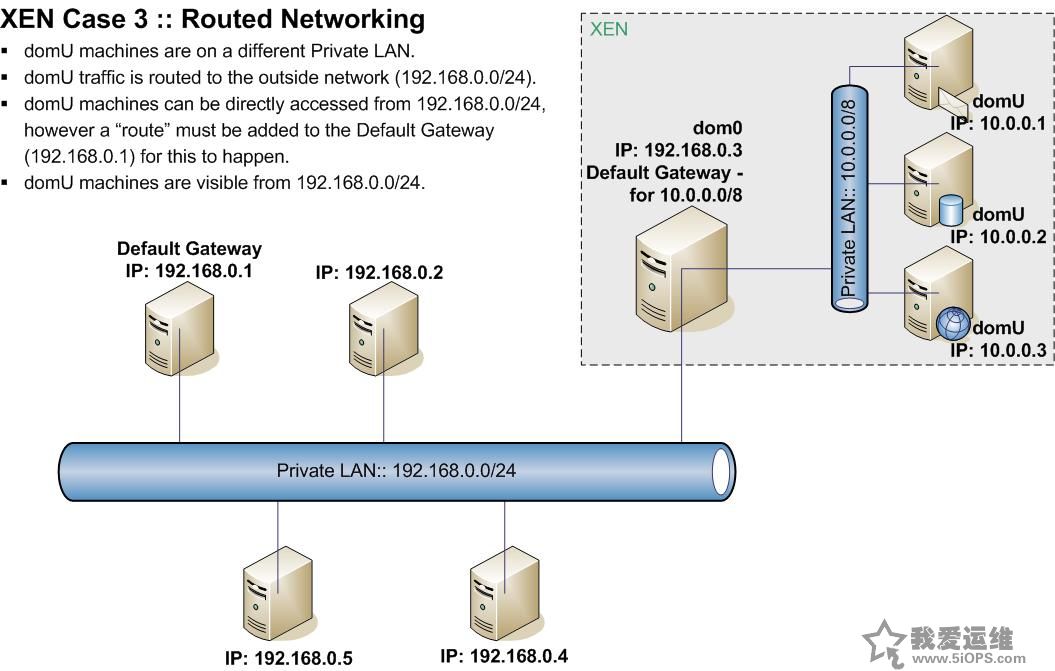
示意图说明如下:
- domU机器处于不同的私有网段中.
- domU的流量是被路由到外部网络(192.168.0.0/24)的.
- domU机器可直接被192.168.0.0/24访问. 但一条路由必须加到默认网关(192.168.0.1)中.
- 192.168.0.0/24 可见domU机器.
此模式与NAT路由模式唯一的区别是domU机器暴露于外部网络中。当VM (10.0.0.1) ssh到外部机器 (192.168.0.5)时,会显示它的原始IP.
配置Xen使用双向路由网络模式
主要配置步骤如下.
- 1. 配置xend-config.sxp
vi /etc/xen/xend-config.sxp (network-script network-route) #(network-script network-bridge) #(network-script network-nat) (vif-script vif-route) #(vif-script vif-bridge) #(vif-script vif-nat)
- 2.配置vm01.cfg (vm配置文件)
vi /etc/xen/auto/vm01.cfg vif = [ 'ip=10.0.0.1' ] #thats all that is required for the networking part.
- 3.配置dom0进行转发
echo 1 > /proc/sys/net/ipv4/conf/all/proxy_arp iptables -t nat -A POSTROUTING -s 10.0.0.0 -j MASQUERADE
- 4. 配置VM自己的网络接口 /etc/network/interfaces
mount /srv/xen/vm01-disk.img /mnt vi /mnt/etc/network/interfaces auto eth0 iface eth0 inet static address 10.0.0.1 gateway 10.0.0.254 netmask 255.255.255.0 xm create /etc/xen/vm01.cfg xm console vm01
- 5. 配置默认网关192.168.0.1到 10.0.0.0的路由
为让192.168.0.0/24 IP地址段的机器可以看到10.0.0.0/8,需要配置增加一条路由. 需要配置在外部网络的默认网关上(192.168.0.1),以当机器查询 10.0.0.0/8 地址时,他们的默认网关可以找到路由记录.
192.168.0.1:~# route add -net 10.0.0.0 netmask 255.255.255.0 gw 192.168.0.3 route #to delete this route: route del -net 172.16.0.0 netmask 255.255.255.0 gw 193.1.99.76
完成.这样所有VMs (10.0.0.0/24) 将可全面互相访问,外部网络(192.168.0.0/24)可通过dom0访问到他们。所有流量会通过dom0进行转发,所有自10.0.0.0/8到192.168.0.0/24的连接都会显示其真实IP地址.
注: 第5步是关键. 没有这一步,连接不能回去.
双向路由模式排障
在Odom0上运行ifconfig 应有如下相似内容:
dom0:~# ifconfig
eth0 Link encap:Ethernet HWaddr 00:50:8B:DC:F7:2B
inet addr:192.168.0.3 Bcast:192.168.0.3 Mask:255.255.255.0
inet6 addr: fe80::250:8bff:fedc:f72b/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:1105 errors:0 dropped:0 overruns:0 frame:0
TX packets:723 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:105354 (102.8 KiB) TX bytes:99490 (97.1 KiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:8 errors:0 dropped:0 overruns:0 frame:0
TX packets:8 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:560 (560.0 b) TX bytes:560 (560.0 b)
vif1.0 Link encap:Ethernet HWaddr FE:FF:FF:FF:FF:FF
inet addr:192.168.0.3 Bcast:192.168.0.3 Mask:255.255.255.255
inet6 addr: fe80::fcff:ffff:feff:ffff/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:194 errors:0 dropped:0 overruns:0 frame:0
TX packets:153 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:13094 (12.7 KiB) TX bytes:25365 (24.7 KiB)
在dom0上运行route 应有如下相似内容:
dom0:~# route Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 10.0.0.1 * 255.255.255.255 UH 0 0 0 vif1.0 192.168.0.0 * 255.255.255.0 U 0 0 0 eth0 default 192.168.0.1 0.0.0.0 UG 0 0 0 eth0
在dom0上运行iptables -L 应有如下相似内容:
dom0:~# iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination ACCEPT 0 -- 10.0.0.1 anywhere PHYSDEV match --physdev-in vif1.0 ACCEPT udp -- anywhere anywhere PHYSDEV match --physdev-in vif1.0 udp spt:bootpc dpt:bootps Chain OUTPUT (policy ACCEPT) target prot opt source destination
在dom0上运行iptables -t nat -L 应有如下相似内容:
dom0:~# iptables -t nat -L Chain PREROUTING (policy ACCEPT) target prot opt source destination Chain POSTROUTING (policy ACCEPT) target prot opt source destination MASQUERADE 0 -- 10.0.0.0 anywhere Chain OUTPUT (policy ACCEPT) target prot opt source destination
在domU上运行ifconfig 应有如下相似内容:
vm01:~# ifconfig
eth0 Link encap:Ethernet HWaddr 00:16:3E:35:B8:A1
inet addr:10.0.0.1 Bcast:10.0.0.255 Mask:255.255.255.0
inet6 addr: fe80::216:3eff:fe35:b8a1/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:153 errors:0 dropped:0 overruns:0 frame:0
TX packets:194 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:25365 (24.7 KiB) TX bytes:15810 (15.4 KiB)
排查与帮助提示
tcpdump
tcpdump是非常有用的工具,它可以看到ip连接与否!
192.168.0.1:~# tcpdump | grep 10.0.0.1
上一篇:教你搭建自己专有的DNS服务器
下一篇:Puppet配置管理架构探讨
评论排行
- ·Windows(Win7)下用Xming...(92)
- ·使用jmx client监控activemq(20)
- ·Hive查询OOM分析(14)
- ·复杂网络架构导致的诡异...(8)
- ·使用 OpenStack 实现云...(7)
- ·影响Java EE性能的十大问题(6)
- ·云计算平台管理的三大利...(6)
- ·Mysql数据库复制延时分析(5)
- ·OpenStack Nova开发与测...(4)
- ·LTPP一键安装包1.2 发布(4)
- ·Linux下系统或服务排障的...(4)
- ·PHP发布5.4.4 和 5.3.1...(4)
- ·RSYSLOG搭建集中日志管理服务(4)
- ·转换程序源码的编码格式[...(3)
- ·Linux 的木马程式 Wirenet 出现(3)
- ·Nginx 发布1.2.1稳定版...(3)
- ·zend framework文件读取漏洞分析(3)
- ·Percona Playback 0.3 development release(3)
- ·运维业务与CMDB集成关系一例(3)
- ·应该知道的Linux技巧(3)




